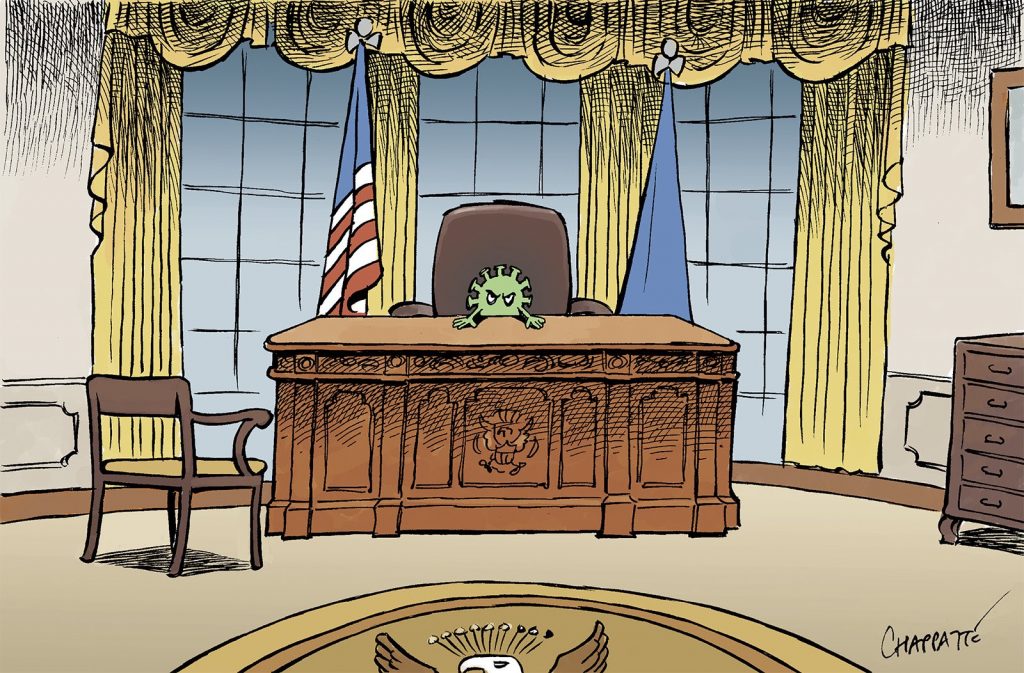
I came face to face with an obvious Ai driven face recognition terminal at the payment desk of a high street retailer.
So not only do they have my payment history and patterns, but my full bio iD (obtained without my permission). Should I submit a subject access request or just let it fly. Maybe I just shop somewhere else now or cover my face on every purchase.
I guess it’s the same approach that cash machines take when your image is taken on every withdrawal.
The most unnerving element was watching the small screen at the payment point with my face being tracked. There are no hiding spots in public spaces so just get used to it.
I did catch a glimpse of a social media campaign encouraging people to go totally offline for the day seemingly in protest of how connectivity dominates our personal lives. The real challenge is we don’t really have the mental toughness to turn it all off.